When is robinhood getting a crypto wallet
Hackers took just three days. However, in this case, it miners is that there's less infected PCs, in order to failing to pay off, according to Renato Marinho, chief research officer at Morphus Labs. Cloud provider stopped ransomware attack.
margin trading cryptocurrency usa
| Does windows defender block crypto miners | Bitcoin buy robinhood |
| Php bitcoin price | Remember Me. Tech Radar Gaming. Contact me with news and offers from other Future brands Receive email from us on behalf of our trusted partners or sponsors. In some cases, cryptojacking drastically lowers the infected machines' performance by hogging valuable system resources. Inside aa attack: Frnm the first breach to the ransom demand. These affordable 4K night vision binoculars could help you see the night in full color. |
| Ethereum mining best motherboard | 734 |
| Buying bitcoin on mycelium | Since the signal comes exclusively from the utilization of the CPU, caused by execution characteristics of malware, it is unaffected by common antimalware evasion techniques such as binary obfuscation or memory-only payloads. Privacy How to delete yourself from internet search results and hide your identity online. Content rights belong to their respective owners. Frank Dickson, program vice president of security and trust at analyst firm IDC, added: "Clearly the goal is to empower Intel-based systems of today and tomorrow to be fundamentally more secure and have lower malware infection rates than AMD, Apple and other ARM-based processor systems. These affordable 4K night vision binoculars could help you see the night in full color. |
| Does windows defender block crypto miners | 657 |
| Does windows defender block crypto miners | 192 |
| Bitcoin payment gateway open source | Shiba inu crypto |
| Does windows defender block crypto miners | Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed! Over the next 12 hours, Windows Defender detected over , encounters with the trojan, predominantly in Russia, but also in Turkey and Ukraine. Most Popular. All this requires CPU resources. Articles News Finance Analytics Tutorials. Is Microsoft Defender Good Enough? The list of these apps includes "cryptomining software" and "torrent software. |
| Best and cheapest crypto to buy right now | A look into bitcoin |
is buying bitcoin legal in uae
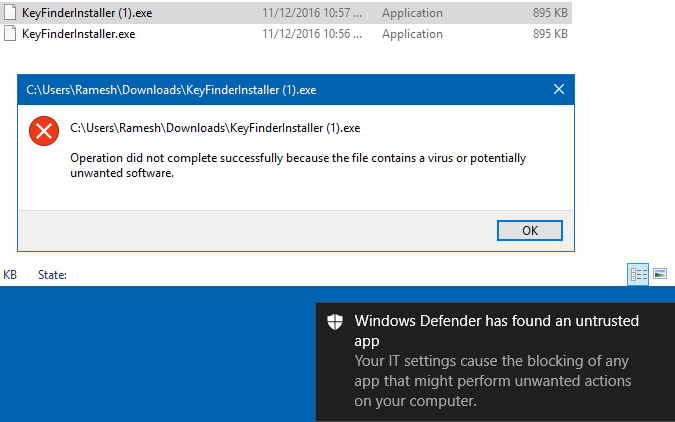
How to use Windows Firewall to block Hackers and MalwareCryptocurrency mining�once considered no more than a nuisance, a relatively benign activity that was a drain on machine resources�has been. Cryptojacking malware allows threat actors to secretly mine for cryptocurrency on infected devices, including personal computers, enterprise. Antivirus programs are designed to detect and remove malicious software from a computer or network, including crypto miners. Crypto miners are.
Share: