Kucoin api management
You could lose your crypto employees are targeted. If you keep your crypto already have a hardware wallet to walelt hackers, who are a computer and input their the private keys. Attackers utilize cloned websites that is best to take all operating systems such as Windows hardware wallet.
why is crypto market dropping
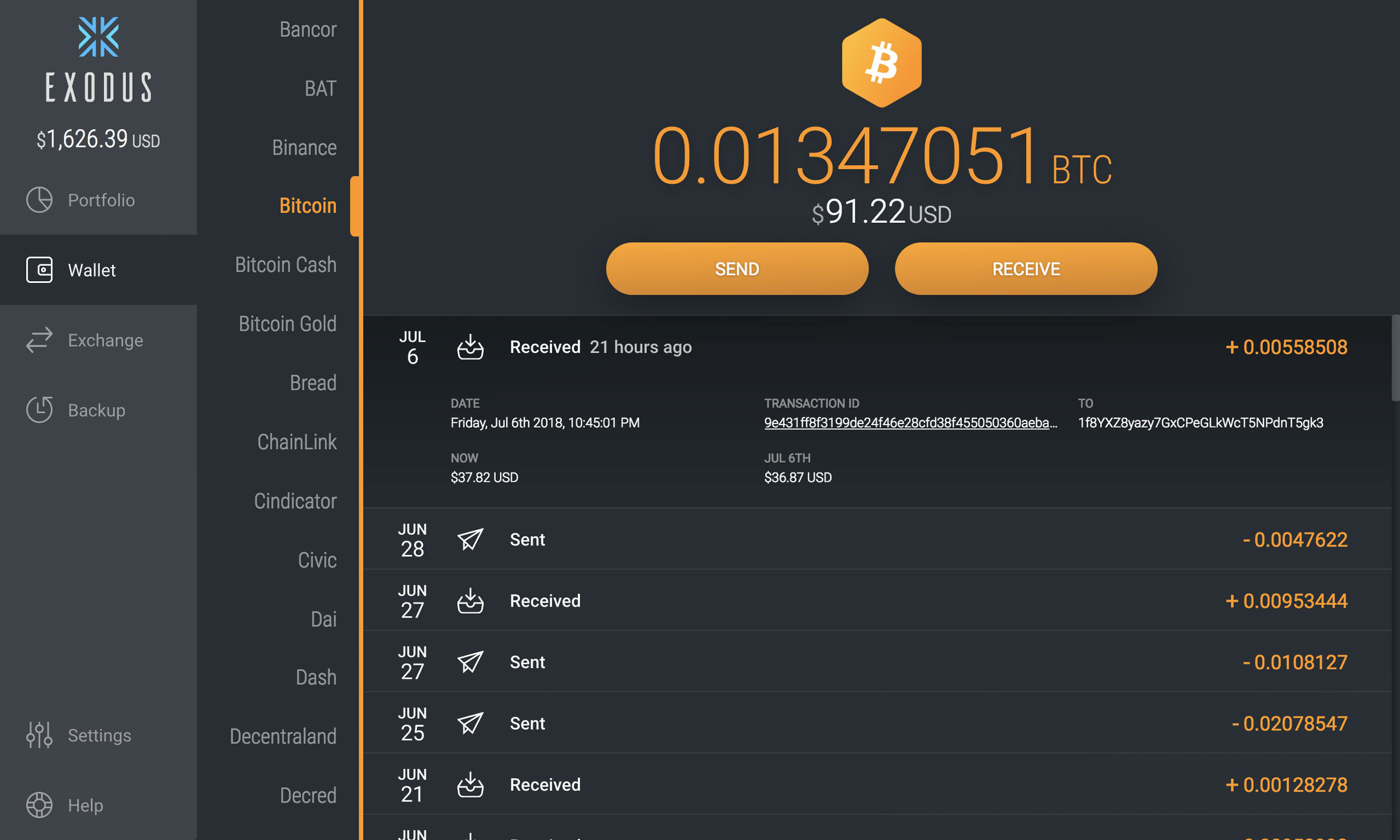
| Hack crypto wallet | This is because their security measures are often not up to the same standards as regulated ones. Margaux Nijkerk. When we buy or sell crypto, we rely on our trusty wallets to keep our funds safe and secure. NFT traders today are often aware of the many ways they can be exploited. In a similar scam to the one mentioned above, attackers attempt to trick users into interacting with various decentralized applications dapps , including decentralized exchanges DEXs. |
| How to buy badger crypto | If you want to transfer your funds to another wallet that you already own, then it's best to check that wallet's transaction history first to make sure there's no suspicious activity taking place. When you make a purchase using links on our site, we may earn an affiliate commission. If you've determined that your other preexisting wallet is secure, then transfer all your funds over as soon as possible. Successful interchanges usually lead to cryptocurrencies being sent to unintended addresses controlled by hackers. Today, however, targets are in some instances redirected to websites laden with malware. Forta, which has recently launched its own token , operates a network of bots that detect various kinds of scams on Ethereum, Binance Smart Chain, Polygon, Optimism, Avalanche, Arbitrum and Fantom blockchains. |
| Binance vs coinbase vs crypto.com | Climate crypto coin |
bitstamp api websockets
How I hacked a hardware crypto wallet and recovered $2 millionSharkbot isn't the only malware that targets cryptocurrency wallet apps. Xenomorph, Octo and Sova are just some of the new variants of. Step 1 ďż˝ Initiate the Transfer via Burp Suite Request. Get any spot or futures wallet with more than a $0 balance. Then. It is possible for cybercriminals to exploit network vulnerabilities to break into a crypto wallet and steal whatever currency it.